The Reach Is the Verification — Geometric Actuation and ShortRank
Published on: April 23, 2026
Slide a bead on an abacus. The bead is not a representation of counting. The bead IS the counting. The position of the bead after you move it is the answer. You did not compute the answer and then store it somewhere. The computation and the storage were the same physical event.
A slide rule does the same thing. Align the cursor and read the hairline. The geometry is logarithmic. Sliding is multiplication. There is no program counter. There is no instruction cycle. There is no step between "compute" and "verify." The position of the cursor IS the answer, and the answer verifies itself by being at that position.
Your hand reaching for a cup does the same thing. The reach is not a representation of intention translated through a symbol layer. The body is the medium in which intention and motion are the same event at different scales.
Call this geometric actuation. The geometry moves, and in moving, the consequence is already present.
In 1945, von Neumann made a choice. Computation could be built two ways.
Build a machine whose geometry is the thing it operates on — an analog circuit, a mechanical integrator, a slide rule. Or build a machine that manipulates symbols representing the thing, with a program counter, a memory, and instruction cycles.
The first class does geometric actuation. The second simulates it. The second won. Substrate independence, scalability, portability — the reasons were sound. The cost was the property. A simulation of geometric actuation is not geometric actuation. The coupling that made the slide rule its own answer lives only in the programmer's head when the calculator emulates it.
This was invisible for eighty years. Nothing the field cared about required the missing property. Files were overwritten. If a log was wrong, you checked it against a second log. Workarounds covered everything.
AI is the first computing application that asks a question workarounds cannot answer: is the thing running at this moment the thing we authorized?
The answer lives only in the class computing gave away.
This is not a moral system. It does not know right from wrong. It does not judge the content of what the AI produces. It is pre-moral — the same way a thermometer is pre-moral. The thermometer does not have an opinion about the temperature. It reads the number. What you do with the number is governance, ethics, policy — a different layer entirely, and genuinely human work.
What it does is tilt the cost of verification.
In a detached-record system, verification is expensive. Every check requires a separate operation — a second program inspecting a first program, a log auditing a process, a human reviewing an output. The cost scales with the complexity of the system being verified. The more complex the AI becomes, the more verification you need, the more budget you burn. When the cost exceeds the budget, verification stops happening. Not because anyone decided to skip it. Because the budget ran out.
When the budget runs out, something else pays. Your brain pays. The symbol grounding problem is this, restated: symbols in detached-record systems cannot touch reality on their own, so they hook onto the nearest autocoincident substrate that can — your nervous system. Your cortex becomes the free verification layer. You read the output. You feel whether it is right. You carry the cognitive load of grounding what the machine cannot ground for itself. That is not collaboration. That is parasitism — the system using your biological substrate as an unpaid verification service.
When verification is free — when the reach IS the verification, when a cache hit confirms correctness as a structural property of the access — the budget arithmetic inverts. The system no longer needs your brain to ground its symbols. Your brain is released from the verification burden. You can use your cognitive budget for decisions instead of for checking. That is the tilt. Not moral. Pre-moral. The conditions under which synergy becomes structurally possible instead of structurally impossible.
This is not what cryptography does. Cryptographic hash chains prove the bytes have not been tampered with. That is tamper-evidence — a property of the first proof (the hash). It does not tell you the system is still doing what it was authorized to do. Role continuity is a different property, in a different class, requiring a different kind of anchor. A signed binary that has drifted from its authorized function is a perfectly signed drift. The signature confirms the bytes. The role has moved. Crypto solves the name problem. This solves the role problem. Different class. Different gap.
The outcome of not closing this gap is drift. Not crash. Not error. Drift — silent, compounding, structurally guaranteed by the class definition. The system renders correct behavior without maintaining it. The verification budget bleeds. The human pays. The dashboard glows green.
ShortRank orders data the way your mind already organizes what it knows: parents before children, all depth-N before any depth-N+1.
When you think of "vehicles," your mind does not search a flat list. You reach for "vehicles" and the children are already there — cars, trucks, boats — because your neurons organized them by co-activation. The parent fires and the children fire with it because they live in adjacent neurons. The reach and the recognition are one event.
Build a toolbox. Heavy tools on the bottom shelf. Sharp tools on the right. Close your eyes. Reach for the heavy hammer. Your hand goes to the bottom left. You did not search. You did not check an index. Finding the hammer was an O(1) operation — because the physical layout of the wood is a rigid cast of the sorting rule inside your head. You know the coordinate because you are the author of the arrangement. The arrangement is the answer.
ShortRank does the same thing in silicon. The compositional address function computes every child's physical address from the parent's address:
BASE + sum(rank x STRIDE)
The parent's address determines where every child lives. Not by looking them up. Not by searching an index. By the geometry of the address space itself. The parent's coordinate contains the children's coordinates the way a trunk contains its branches — structurally, not by reference.
When you reach from a parent to a child in ShortRank, the reach IS the verification. If the child is at the computed coordinate, the relationship held. Cache hit. The data is where the hierarchy says it should be. If the child is NOT at the computed coordinate — cache miss. The silicon already knows. The relationship broke. The data moved from where the hierarchy placed it. No separate check. No audit trail. No second operation. The reach and the verification are the same physical event.
A cache hit is not just "the data arrived fast." A cache hit is a correctness proof. The data is at the address the compositional function computed. Position IS meaning. The hit confirms the meaning held.
A cache miss is not just "the data arrived slow." A cache miss is a correctness violation. The data is not where the hierarchy placed it. Something moved. The displacement is the measurement. The latency penalty is the receipt.
The arrangement is the answer. There is no second step.
When data crosses a cache-line boundary — when a reach from parent to child leaves the gestalt block where the parent lives — the processor does three things at once:
- The data arrives (the retrieval).
- The hardware performance counter increments (the measurement).
- Energy dissipates (the thermodynamic record the universe cannot erase).
These are not three events. They are one event at three scales. The retrieval, the measurement, and the receipt are the same physical motion. No software participated. No instruction executed. The geometry of the address space produced the signal by being crossed.
This is Landauer's principle in action. Erasing a bit costs kT ln 2 of energy. Crossing a cache-line boundary dissipates energy the universe tracks. The hardware counter reads the crossing. The energy is the proof that the crossing happened — and the universe does not allow that proof to be deleted, because deleting it would cost at least as much energy as the crossing itself.
The record is the event. The reach is the verification. The heat is the receipt.
One property verified. One physical event. One thermodynamic anchor that no software can forge, because the anchor is not in software. The anchor is in the geometry of how the data is laid out, in the physics of what happens when a cache line is crossed, and in the thermodynamics that makes the crossing irreversible.
Your grandmother at the door. She does not search a database. She does not run a facial-recognition algorithm. Decades of co-located neurons fire together because they were wired together by decades of seeing you. The recognition is the retrieval. One event. If someone else is wearing your face, the mismatch fires before she can articulate why — because the neurons that should fire together did not fire together. The cache miss is the detection. The detection is the reach that failed to land.
The book makes the same argument in five sentences. From Tesseract Physics, § The Qualitative Cliff:
Grip is verification. The reach IS the proof. And the proof is that you can keep reaching — into the unknown, into the irreducible, into the surprise — and the floor holds. Every time. At every coordinate. Because the position IS the meaning, and the meaning persists.
Every organism that maintains contact with reality runs this architecture. The cerebellum corrects your balance at 10 milliseconds — before your cortex knows you stumbled — because the predictive model and the motor output share the same substrate. The prediction and the correction are one event. Reach and verification, fused in the physics of adjacent neurons. Biology calls this proprioception — knowing where your body is without looking.
ShortRank gives silicon the same property for meaning. Call it semantic proprioception — knowing where the data is without looking it up, because the arrangement that placed the data IS the knowledge of where the data is. The compositional address function is the nervous system. The stride inequality is the wiring. The cache hit is the recognition. Your grandmother does not look you up. ShortRank does not look the data up. Both reach, and the reaching is the knowing.
The mind that organized the hierarchy already knows where to reach for the children. The reach is not a search. It is a geometric consequence. And the consequence verifies itself by being at the coordinate the geometry requires.
Everything else — the XOR gate, the hardware counter, the trust artifact, the autocoincidence theorem — follows from this one property: the reach and the verification are the same physical event.
Geometric actuation is not a simpler form of computation. It is the class below computation. It is how the universe already works.
Gravity does not compute trajectories. Mass curves spacetime and objects follow the geometry. Chemistry does not compute reactions. Electron orbitals have shapes and the shapes determine what bonds. Evolution does not compute fitness. Organisms fit the environment's geometry or they do not. In every case, the geometry moves, and in moving, the consequence is already present. No program runs. No instruction executes. The structure updates and the result is the structure.
Computation is an abstraction of this. In 1945, von Neumann chose to simulate geometric actuation with symbols — program counters, instruction cycles, memory addresses decoupled from meaning. The simulation won because it was portable, scalable, substrate-independent. The cost was the property. A simulation of geometric actuation is not geometric actuation, the same way a map of a territory is not the territory. The map can be overwritten without the territory knowing. The territory cannot.
Every computer built since 1945 operates in the simulation. Every verification system built on top of it inherits the gap between the map and the territory. Software checking software is maps checking maps.
The patent does not build a better map. The patent stops the simulation at one surface of silicon and lets the geometry do what geometry does.
Look at the figure.
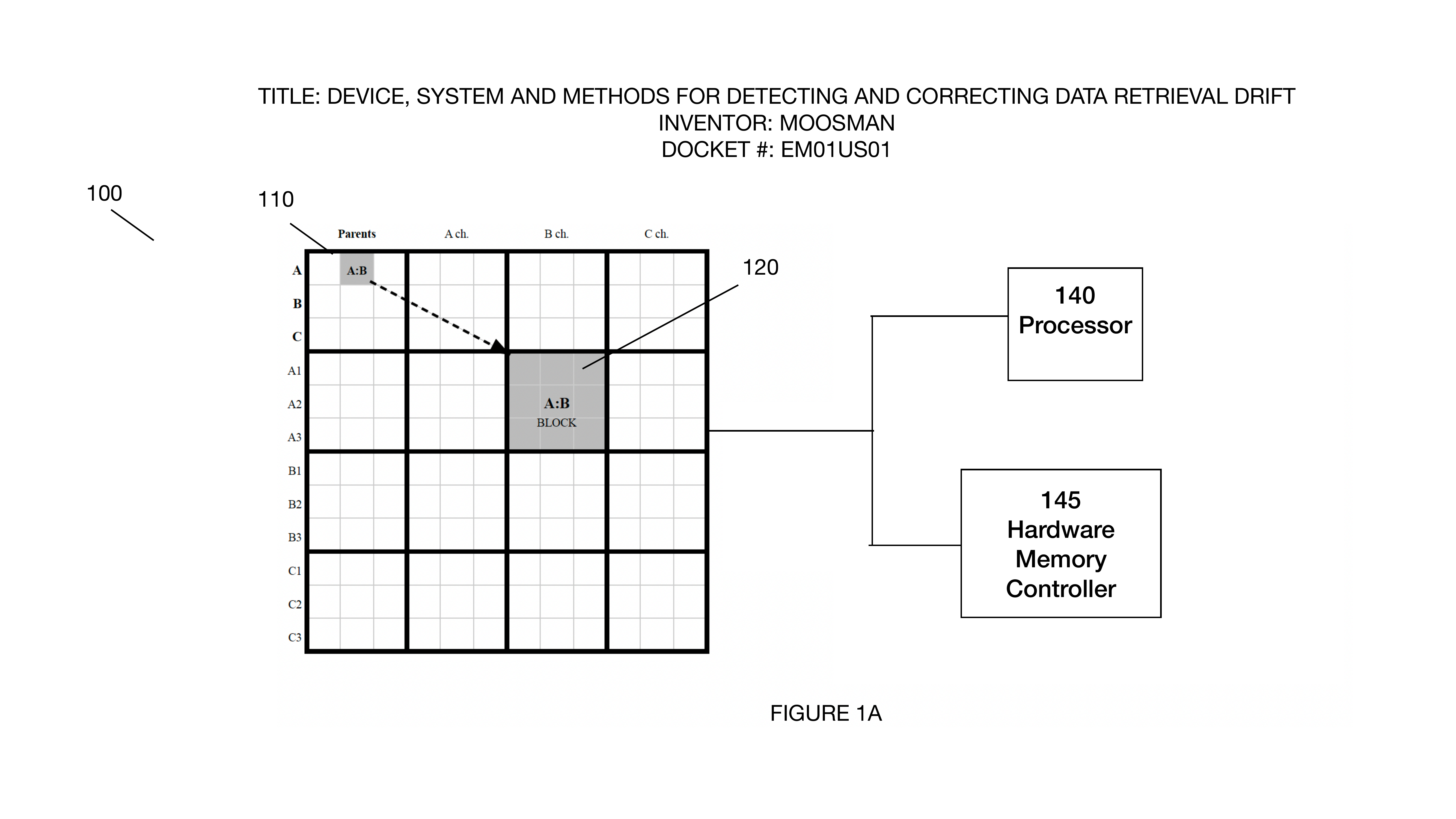
FIG 1A from US 19/637,714. The memory grid (100). Parents on the left axis (A, B, C). Children across the top (A.ch, B.ch, C.ch). The shaded region (120) is one gestalt block — one cache-aligned region whose data shares a common parent. The dotted arrow is a reach that crosses from one block to another.
The grid (100) is the hierarchy, laid into physical memory. Parents on the left axis: A, B, C. Children across the top: A.ch, B.ch, C.ch. The shaded block (120) is one gestalt block — a cache-aligned region whose data elements share a common hierarchical parent. The thick lines between blocks are gestalt gaps — cache-line boundaries.
The compositional address function computed every position: BASE + sum(rank x STRIDE). Whatever process organized the hierarchy — human mind, machine process, algorithm — that process decided A is parent of A.ch, B is parent of B.ch. The address function took that decision and produced a physical address for each element. The parent's address determined the children's addresses. The children's determined the grandchildren's. All the way down. Self-similar at every depth, because the composition is the same rule at every scale.
The gestalt gaps land at the same positions as the parent-child boundaries. Not approximately. Exactly. The stride constants are computed to align semantic boundaries with cache-line boundaries. Whatever process decided where the categories begin and end also decided — in the same act — where the hardware will detect a crossing.
Now follow the dotted arrow in FIG 1A. A reach from an element in one gestalt block to an element in another. That reach crosses a gestalt gap. When it crosses:
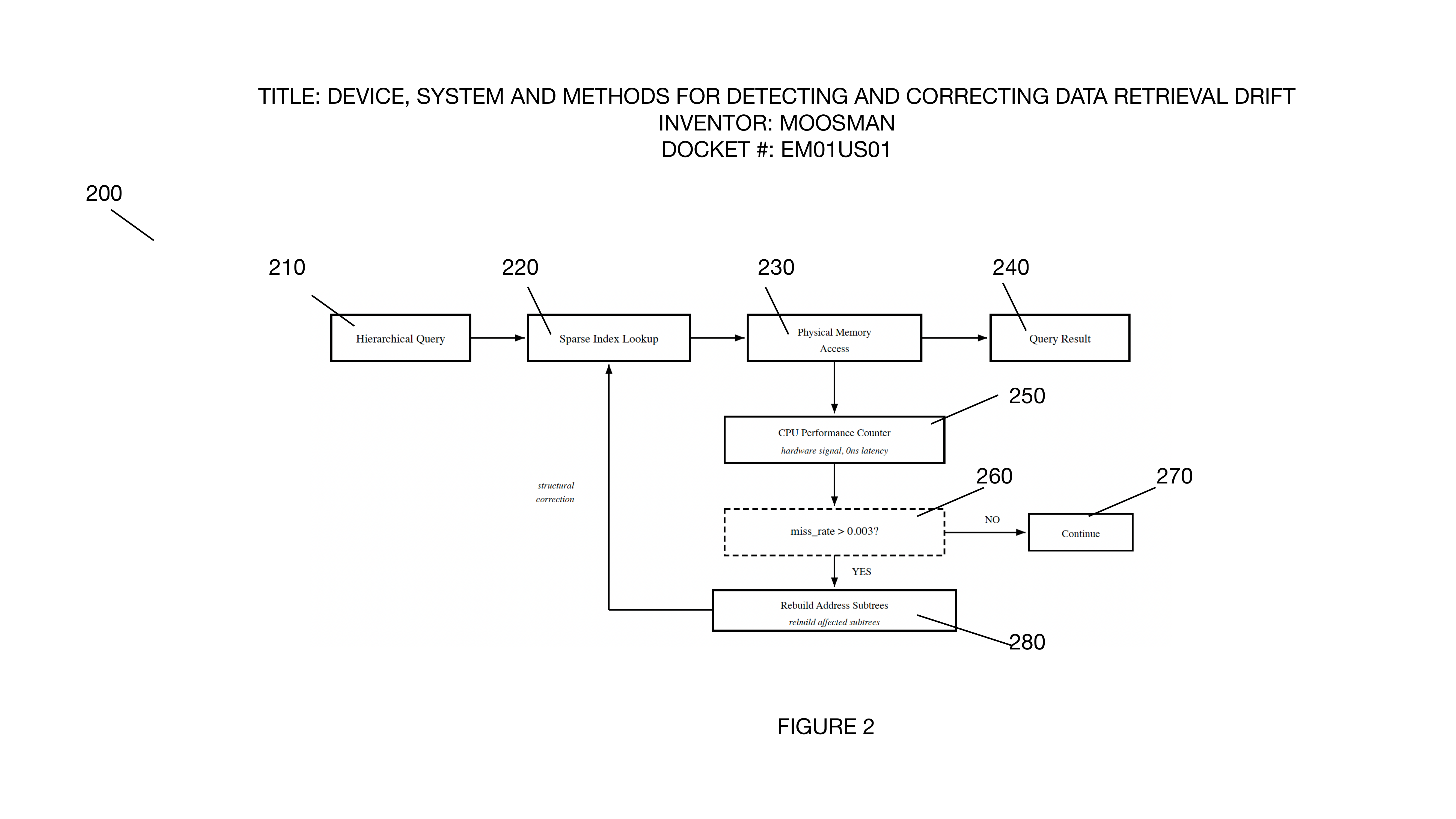
FIG 2 from US 19/637,714. The GDC (Geometric Drift Control) loop. The CPU Performance Counter (250) detects the crossing. If the drift rate exceeds k_E = 0.003, the system rebuilds the address scheme (280) to restore positional equivalence.
The reach (210 → 220 → 230) arrives at the Physical Memory Access. The CPU Performance Counter (250) — hardware, not software — detects the boundary crossing. The counter increments. Energy dissipates. The universe records the crossing.
If the data is where the compositional function placed it — cache hit. The reach and the verification were one event. The relationship held. Continue (270).
If the data is not where the function placed it — cache miss. The reach detected the displacement. The drift rate crosses the threshold (260). The GDC loop fires Rebuild Address Scheme (280) — the system physically reorganizes the memory to restore positional equivalence.
No program decided whether the data was correct. The geometry decided. The geometry decided at the moment the organizing process placed the data — the same way a key's geometry decides whether it fits a lock at the moment the key is cut. Pre-computational. The class below computation.
The index is not in the matrix. The index IS the matrix. The hierarchy is not metadata about the data. The hierarchy is the physical address layout. The organizing act and the verification geometry are the same object. This is how autocoincident role verification connects information to reality — by making the organizing process's fingerprint identical to the verification geometry, so there is no gap for drift to live in.
Whatever process legitimately organized the hierarchy did not build a verification system. Whatever process legitimately organized the hierarchy IS the verification. The silicon carries the fingerprint. The fingerprint carries the boundaries. The boundaries carry the detection. Every reach is a check. Every check is a structural consequence of the legitimate placement. The legitimacy of the placement is the verification. The illegitimacy of the displacement is the signal.
The class where organization and verification are the same structure: autocoincident. The class where they are separate — where maps check maps and the territory is silent: detached-record. The compositional address function is the bridge between classes. One-way. Abstraction is spontaneous. The reverse cannot be done by accumulating software. It can only be done by anchoring the structure to the physics — making the semantic coordinate identical to the physical address, so that separating them requires moving the coordinate, which the hardware detects as a cache-line crossing, which dissipates energy the universe cannot erase.
That is not computation. That is the class below computation. The class the universe runs on. The class computing gave away in 1945. The class the patent restores at one load-bearing surface.
The compositional address function is a direct mirror of whatever process organized the hierarchy. The hierarchy is the fingerprint. The fingerprint is the geometry. The geometry is the verification. Pre-computational. FIG 1A is the geometry. FIG 2 is the detection loop. The reach from parent to child IS the verification — one event, one class, one anchor connecting information to reality.
The patent. US 19/637,714 — 36 claims, Track One. Section [0182]: "A cache hit confirms not only that the data is present but that it is the right data at the right coordinate. A cache miss reports not only a latency penalty but a correctness violation." The compositional address function, the gestalt blocks, the GDC control loop — all of it exists to make one thing true: the fetch IS the verify. The annotated thread documents the argument tested in public. The autocoincidence theorem names the class distinction. The move is the reach.
The geometry moves, and in moving, the consequence is already present. The reach is the verification. The heat is the receipt. The mind that organized the hierarchy already knows where to reach for the children — because the mind that organized the hierarchy IS the verification, carried in silicon, at every depth, by the same compositional rule.
US 19/637,714 — 36 claims — Track One. Filed April 2, 2026.
Ready for your "Oh" moment?
Ready to accelerate your breakthrough? Send yourself an Un-Robocall™ • Get transcript when logged in
Send Strategic Nudge (30 seconds)